What is https?
Hypertext Transfer Protocol Secure is in short referred to as HTTPS. Sites running over HTTPS will generally have a redirect in place so even if you type in HTTP:// it will redirect in order to deliver over a secured connection. Transmission Control Protocol (TCP) is also used by HTTPS in order to send and receive data packets, but it does so over port 443, within a connection encrypted by Transport Layer Security (TLS).
What does https Mean?
HTTPS has been established to sanction secured transactions and authorization over the web. Exchanging information, like credit card numbers or access, requires security to avoid unauthorized entry via HTTPS. HTTPS makes it more difficult for the NSA, hackers, and others to track users. The protocol ensures that the data does not get transmitted in plain-text format, which is indeed much easier to eavesdrop on.
What is the Difference Between http and https?
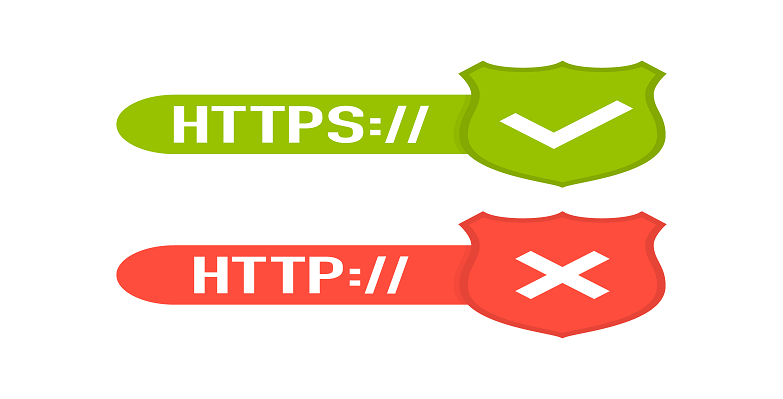
- HTTP is unsecured while HTTPS is secured
- HTTP does not need require domain validation, whereas HTTPS needs at least domain validation and certain certificates even require legal document validation.
- HTTP sends data over port 80 and HTTPS uses port 443
- No encryption in HTTP, with HTTPS the data is encrypted before sending
- HTTP works at the application layer, while HTTPS operates at the transport layer
- HTTP URL in your browser’s address bar is HTTP:// and the HTTPS URL is HTTPS:
- No SSL certificates are needed for HTTP, with HTTPS it is essential for you to have an SSL certificate and it should be signed by a CA.
How https works
HTTPS is capable of keeping your stuff a secret by encrypting it as it moves between the website’s server and your browser. This guarantees that anyone listening in on the conversation will not be able to anything. This could include your hacker, ISP, snooping governments, or anyone else who succeeds in positioning themselves between the web server and you.
For a very long time, SSL was the standard protocol used by HTTPS. The latest version of SSL is presently called Transport Layer Security (TLS) but they are basically the same thing. You need three things to encrypt data:
- The data you want to encrypt
- An encryption algorithm (a math function that “garbles” the data)
- A unique encryption key (just a long string of random text)
- You plug the data and the key into the algorithm and what comes out the other side is cipher text.
To decrypt the cipher text on the other end, you just have to reverse the process with the same key and it reverses the encryption, restoring the original form of the data. It is the secrecy of the encryption key that allows the whole process work. Only the intended recipients of the data should have it, or else the purpose is defeated.
When you use the same encryption key on both ends it is known as symmetric encryption. This is what is used by your home WiFi. You have only one key, or “password”, which you plug into both your laptop and your wireless router. However, it becomes more complicated when connecting to a website on the public internet. Symmetric encryption, by itself, will not work because you don’t control the other end of the connection. This problem is resolved with the help of asymmetric encryption. Asymmetric means you are using two different keys, one to decrypt and one to encrypt. This is called Public Key Cryptography as this is how establish secure connections further established on the public internet.
Why does Google like HTTPS so much?
Google made an announcement that it will provide sites using encryption a higher rank in its search algorithms. It specifically singled out HTTPS, which it characterizes as “industry-leading security.”
HTTPS is already being employed as the default for Google sites, which scrambles data as it passes from Google’s servers to the user’s computer. It was launched in 2011 as the default for Gmail, its webmail service. For now, Google is using HTTPS as an extremely lightweight signal—impacting lesser than 1% of worldwide queries, and carrying less weight than other signals such as high-quality content. According to Google, this will probably change in the future. In its blog, Google stated that it is keen on encouraging all website owners to switch from HTTP to HTTPS in order to keep everyone safe on the web.
Reasons Behind the HTTPS Movement
Websites with HTTPS are ranked higher in the Google search results. This should be known by marketers involved in search engine optimization. Websites that are not secure have no place in the top search engine results pages (SERPs). This is Google’s method of incentivizing good security practices, however, they don’t just reward good behavior and hence punish the ones that are not taking necessary precautions.
Deciding to Wait Can Damage Businesses
Visitors may not want to stay on a website when they see a warning in their Chrome browser but Firefox and several other browsers will follow their lead. This is particularly true for e-commerce websites as they may suffer the most. Users may not be interested in purchasing from a website when there is an insecure warning even if the checkout page is secure.
SSL does not just protect dynamic content such as user logins, e-commerce, and sensitive form data. Some people may even argue that their website is static with no sensitive data or login forms, hence there is no reason for them to use HTTPS. This myth is however incorrect. Browsers and search engines not only favor sites using HTTPS, but SSL also prevents pages from getting tampered with while in transit. In the security world, this is called a man-in-the-middle attack.
Mixed Content Warnings – Not Secure
It is essential for you to set up SSL correctly without mixed content that could compromise security. Mixed content occurs when resources on the page are not coded and pulled over HTTPS. This can result in information leakage. Fixing mixed content can also be a difficult process, and this is mostly the reason why websites with valid SSL certificates comprise of errors next to their padlock icon.
Free Comodo SSL and the cWatch Pro (Web Application Firewall)
Comodo Free Certificate is a fully functional Digital Certificate valid for 90 days and is as trusted as the paid SSL certificates. This highlights the fact that the free certificate is trusted and recognized by 99.9% of all devices and browsers and can instantly go to work securing your website. Your visitors will be able to see the golden padlock and will not see security warnings.
Benefits of Using Free SSL Certificate:
- Issued online in minutes with no delays or paperwork
- Highest strength 2048 bit signatures/256 bit encryption
- Signed from the same trusted root as paid certificates
- Recognized by all major devices and browsers
- SSL Certificate at zero cost for 90 days (other CAs only offer 30 day free trials)
Comodo’s Fully-Managed Web Application Firewall (WAF)
cWatch, developed by Comodo, is a Managed Security Service ideal for websites and web applications that incorporate a Web Application Firewall (WAF) provisioned over a Secure Content Delivery Network (CDN). This is a fully managed solution from a Cyber Security Operation Center (CSOC) staffed with certified security analysts and is powered by a Security Information and Event Management (SIEM) capable of leveraging data from more than 85 million endpoints in order to detect and mitigate threats even before they occur.
Comodo cWatch Pro offers the Following Features:
- 24/7 Cyber security operations center
- Managed web application firewall
- Content delivery Network
- Malware detection and removal
- Security information and event management
- Technical support
How Does a Managed WAF Work?
As HTTP/HTTPS requests are sent to your website, Comodo’s WAF executes the task of intercepting and inspecting them, followed by automatically stripping out any malicious requests prior to them having a chance to reach your server. The most important part is that real-time threat mitigation is offered by Comodo’s WAF’s virtual patching and hardening engines without impacting your website.
With Comodo’s Managed Web Application Firewall You Will Be Protected Against:
- Bad Bots
- Hacker Attacks
- OWASP 10 Threats
- DDoS Attacks
- Spam Attacks
- Zero Day Attacks
- Brute Force Attacks
Related Resources :